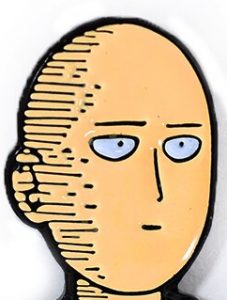
This week I was reading more into the papers I have previously mentioned to better understand the type of attacks there are and how they affect callers. A project report had a topic about “Telephony Harassment/DOS on Wi-fi Calling services” which purpose was to validate on how unsecured Wi-Fi networks cannot defend against Address Resolution Protocol (ARP) spoofing. This is helpful for me because it allows me to implement the attacks that were mentioned in the project report and help figure out a way I can defend against ARP spoofing. ARP spoofing is a type of attack that sends false information to a local area network or router. Below is just an illustration of how an attacker is able to attack their victim.  The adversary ARP spoofs both the router and phone (victim’s device) and is allowed to read the traffic of the victim’s device since the phone is tricked by the fake certificate that ARP spoof has put on the victim’s phone and router. In this case, I was reading the packets of the iPad which is my victim.
The adversary ARP spoofs both the router and phone (victim’s device) and is allowed to read the traffic of the victim’s device since the phone is tricked by the fake certificate that ARP spoof has put on the victim’s phone and router. In this case, I was reading the packets of the iPad which is my victim.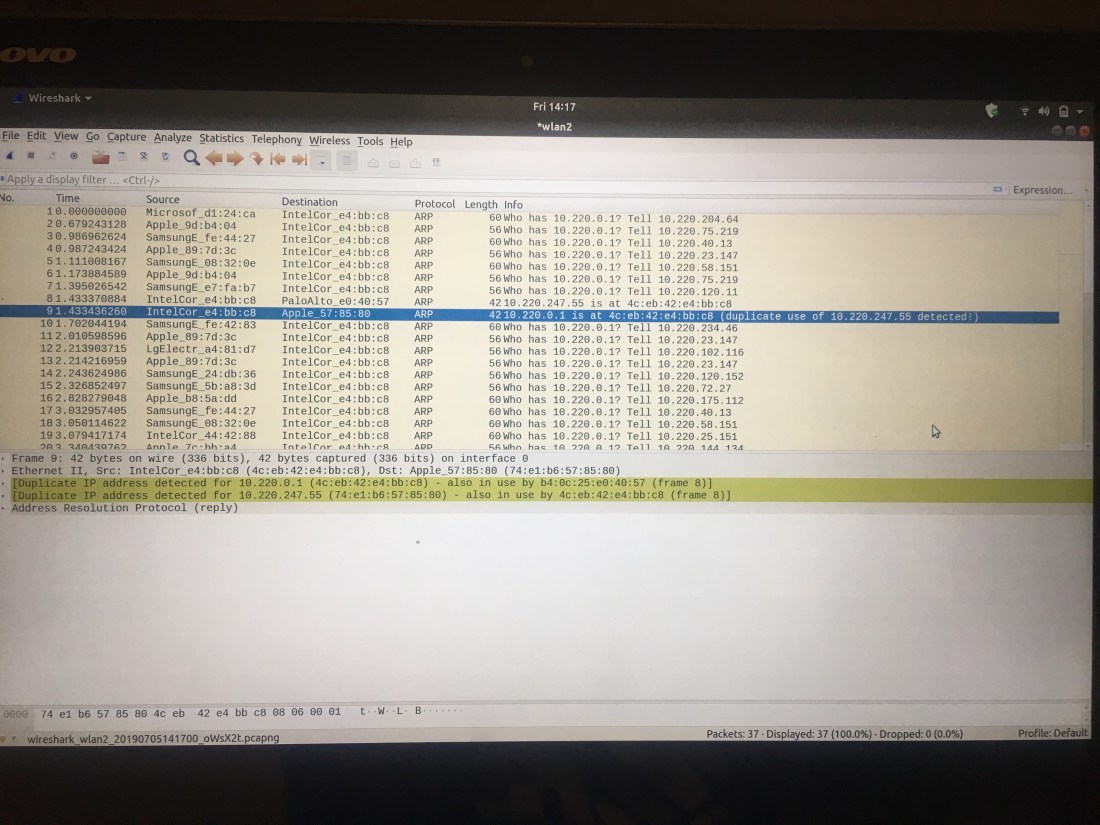 In the picture above, currently only ARP protocol is being filtered and the specific traffic that I highlighted and the one above says those IP addresses are going to a certain MAC address meaning they are both being ARP spoofed by the laptop I am using. This gives permission to the laptop I am using to read any traffic that is going through the iPad.
In the picture above, currently only ARP protocol is being filtered and the specific traffic that I highlighted and the one above says those IP addresses are going to a certain MAC address meaning they are both being ARP spoofed by the laptop I am using. This gives permission to the laptop I am using to read any traffic that is going through the iPad.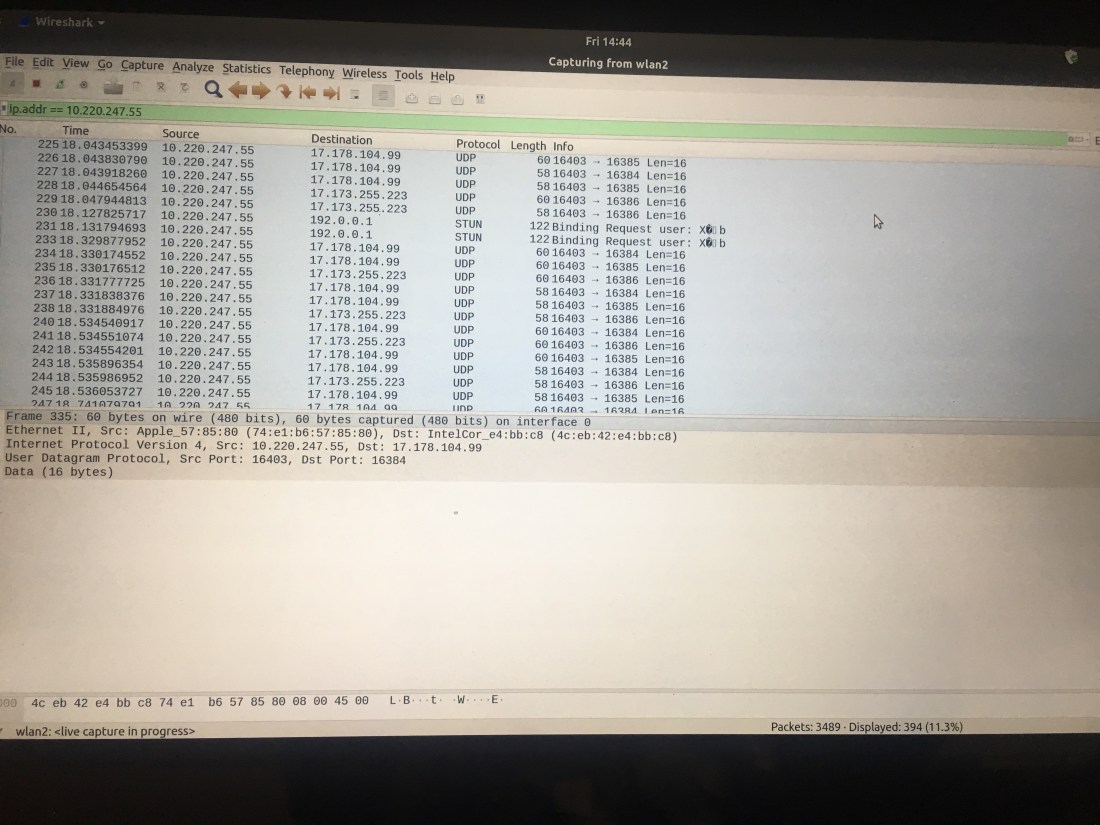 In this picture, now the IP address of the iPad is being filtered and when the call was going on all of these User Datagram Protocol (UDP) packages, which are protocols that establish low-latency and loss-tolerating connections between applications on the internet. There are some Session Traversal Utilities for NAT (STUN) showing up too, which is a protocol that is used for transversal network address gateways in applications that involve real-time voice.
In this picture, now the IP address of the iPad is being filtered and when the call was going on all of these User Datagram Protocol (UDP) packages, which are protocols that establish low-latency and loss-tolerating connections between applications on the internet. There are some Session Traversal Utilities for NAT (STUN) showing up too, which is a protocol that is used for transversal network address gateways in applications that involve real-time voice.